🎯 Project Vision #
The goal was to move beyond traditional hosting and engineer a production-grade web environment that prioritizes security, persistence, and privacy. This project serves as a live demonstration of my ability to manage the full technical stack—from the hypervisor to the public domain.
🏗️ Architecture & Technical Stack #
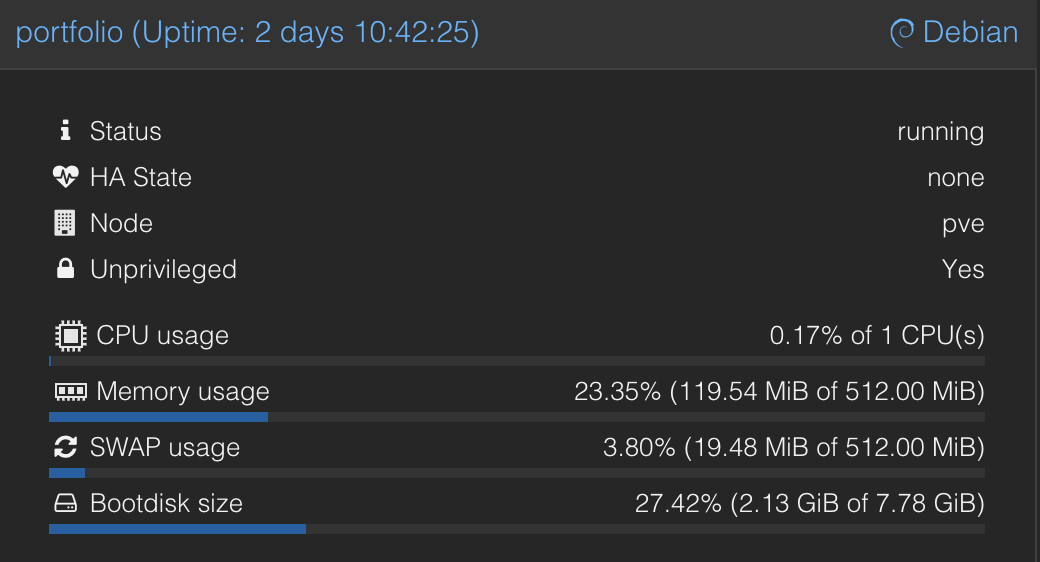
- Hypervisor: Proxmox VE (LXC) — Utilized for lightweight, isolated containerization.
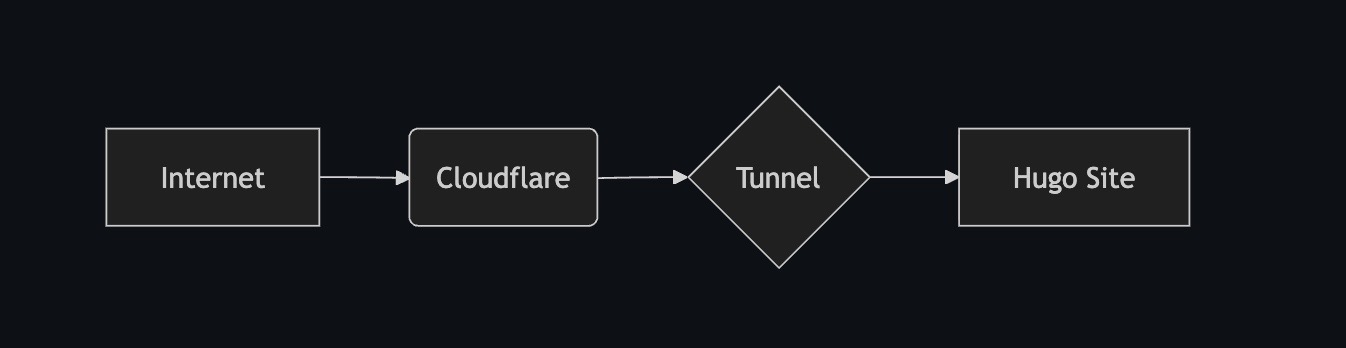
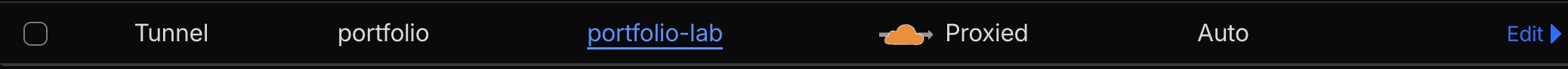
- Networking: Cloudflare Tunnel (Argo) — Provides “Zero-Trust” ingress, exposing the site without opening firewall ports or leaking my home IP.
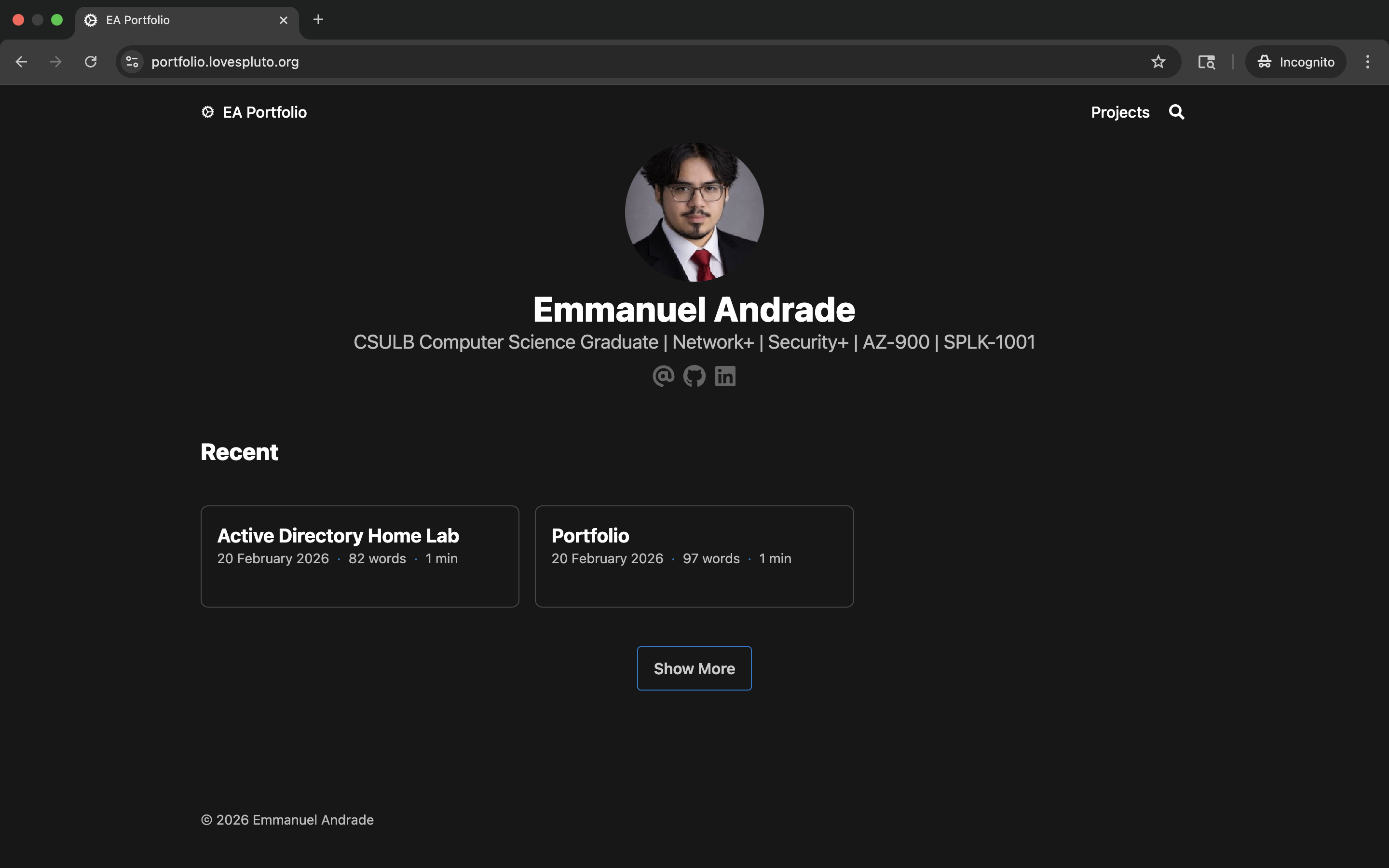
- Web Engine: Hugo (Extended) — A high-performance static site generator utilizing the Blowfish theme.
- OS: Debian 12 — Hardened Linux environment managed via SSH.
🛠️ Key Implementation & Problem Solving #
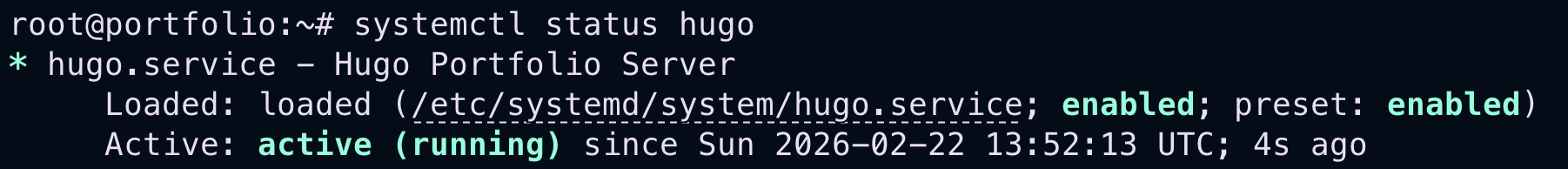
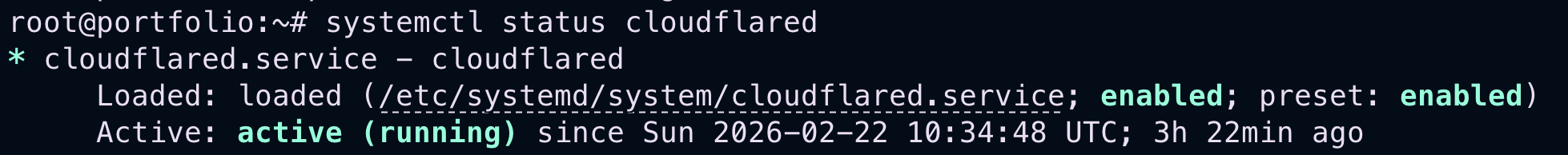
1. High Availability via Systemd #
I transitioned the environment from interactive testing to a persistent production state by creating custom systemd unit files. This ensures that both the web server and the network tunnel auto-start on boot and recover instantly from failures.
2. Operational Security (OPSEC) & Sanitization #
A critical phase involved a “History Sanitization” audit. I purged internal network identifiers (IPv4 192.168.x.x) from the Git history and the Hugo build artifacts to ensure zero information leakage to the public.
🔒 Security Hardening #
- No Inbound Ports: The environment has zero open ingress ports; the Cloudflare daemon creates an outbound-only connection to the edge network.
- Artifact Integrity: Implemented a strict
.gitignorepolicy to prevent the leakage of sensitive build metadata and local file paths. - Persistence: Configured
Restart=alwayspolicies for all services to mitigate downtime.
📈 Professional Takeaways #
- Security-First Mindset: Demonstrated through the proactive sanitization of the version control history.
- Infrastructure Ownership: Managed the end-to-end lifecycle from provisioning hardware to configuring public DNS.
- Resilience: Successfully troubleshot and resolved “502 Bad Gateway” and network binding issues using system-level tools.